12.81 MB
Android 10.0+
412
x86_64, arm64-v8a, armeabi-v7a, x86
Verified safeScanned with ClamAV, APKiD, and Quark-Engine. No threats detected.
Screenshots
Description
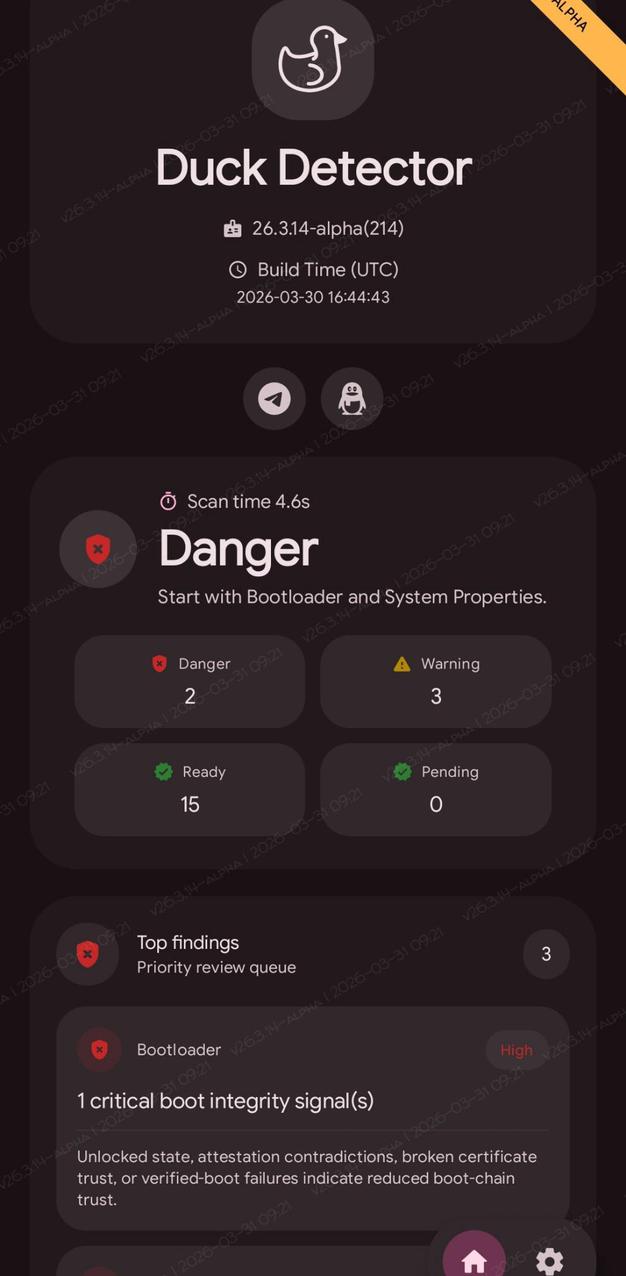
DuckDetector is an Android security inspection app focused on local, device-side evidence collection for root-related tampering, runtime hooking, mount manipulation, attestation trust, and virtualized execution environments.
The project combines a Jetpack Compose UI, modular Kotlin feature packages, and native C++ / assembly probes to surface detector cards with structured findings, method coverage, and scan-state summaries.
Highlights
Modular detector architecture with feature-specific repositories, mappers, view models, and card UIs.
Native startup preload through a transparent NativeActivity launcher for early mount and virtualization evidence collection.
Native runtime probes implemented in C++ and arm64 assembly where timing, syscall, or mount visibility matters.
Cross-process and isolated-process consistency checks for stronger runtime validation.
Dashboard aggregation with per-detector status, top findings, loading states, and detailed drill-down cards.
Mostly local, offline inspection. Network access is only used when the user allows online TEE revocation checks in Settings.
Detector Modules
The current app includes the following major detector areas:
Module Focus
Bootloader Bootloader unlock state and related security posture
Custom ROM ROM fingerprints, platform-file fallbacks, and ROM indicators
Dangerous Apps Installed app corroboration for known risky packages
Kernel Check Kernel build and runtime consistency signals
LSPosed Java-side and native LSPosed / Xposed runtime evidence
Memory Runtime hook residue, suspicious mappings, and loader visibility
Mount Mount tables, mount consistency, startup preload findings, overlay signals, and namespace anomalies
Native Root Native root-runtime traces, corroborated residue paths, and low-level system anomalies
Play Integrity Fix Property spoofing and related runtime consistency checks
SELinux SELinux mode, policy, audit integrity, and context consistency
SU Root binary and runtime root-context indicators
System Properties Property consistency, native snapshots, and raw property-area residue
TEE Key attestation, certificate chain analysis, revocation checks, StrongBox, and RKP signals
Virtualization Emulator / guest / translation / host-app / consistency / honeypot evidence
Zygisk Zygisk state, FD traps, linker residue, and cross-process evidence
Supporting app areas such as dashboard, settings, and deviceinfo provide aggregation, user controls, and device context.
Rate this app
Ratings & reviews
No reviews yet.